Intel evaluated the impact of Meltdown patches and Specter on processor performance (tests)

Intel promises to issue fixes for Meltdown and Specter vulnerabilities for all its processors by the end of January. This can slow down the work of computers, but the results of the company's own tests show that in the case of chips of the last generation, the performance drop in most tasks will be minimal.
Not everything is so bad
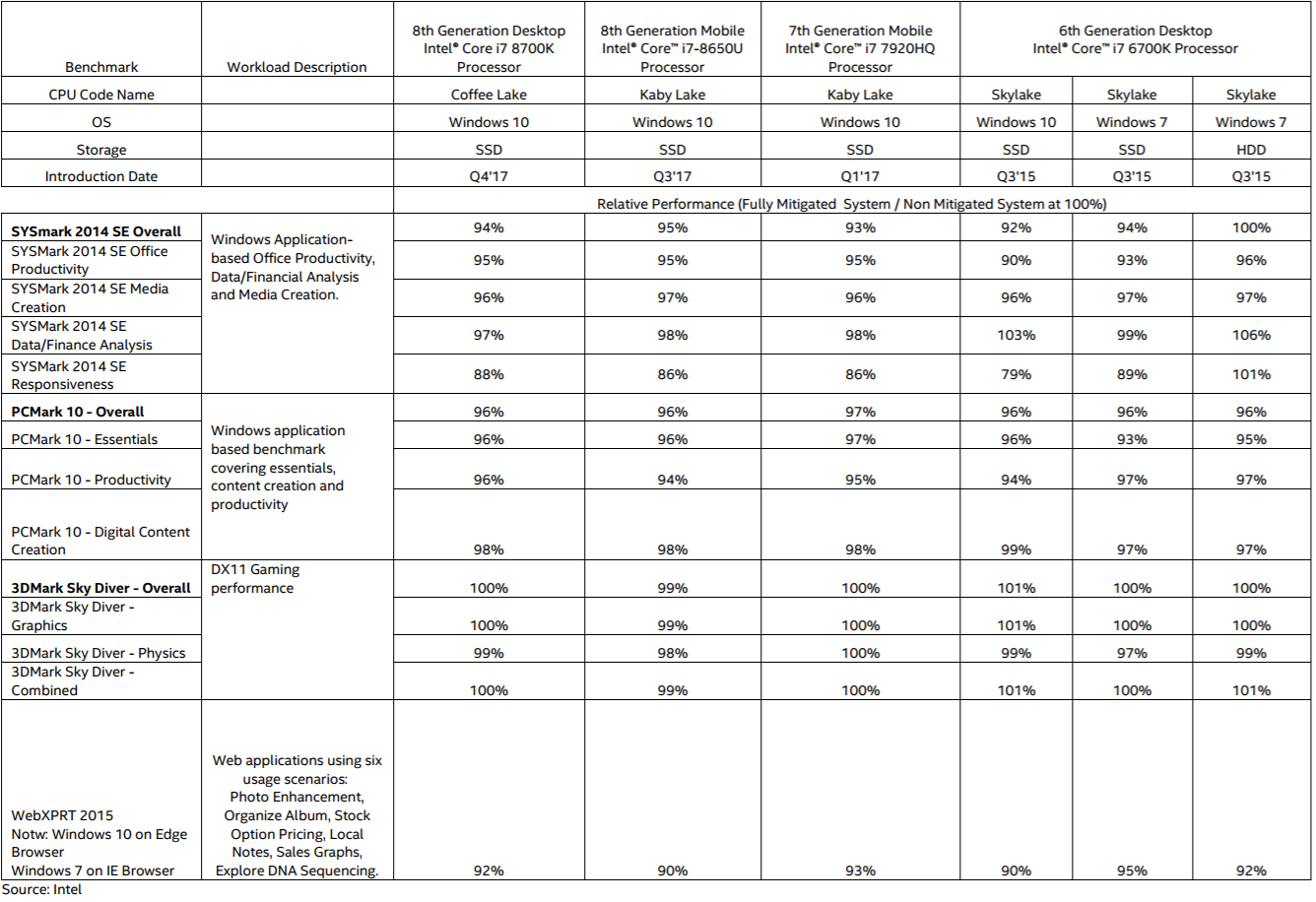
The results in synthetic and semi-synthetic benchmarks reflect typical PC usage scenarios. The list includes the chips of the last three generations (Coffee Lake, Kaby Lake and Skylake): Core i7-8700K, Core i7-8650U, Core i7-7920HQ and Core i7-6700K, which were additionally tested on Windows 7 systems and hard disk. The maximum decrease is observed in web applications with heavy JavaScript operations, as well as in the SYSMark 2014 SE Responsiveness test, which simulates all performance bottlenecks (application launch speed, file openings, multiple browser tabs, data encryption and archiving, multitasking and so on ).
The average user will not notice a significant slowdown in common tasks, although we have not seen the tests of older chips. Data on mobile and desktop solutions released over the past five years will appear in the coming weeks. From day to day, Intel will also publish the results for some server chips (and they will not be so optimistic due to heavy use of I / O).
Difficulties with updates
As vulnerability fixes were prepared in a hurry, there were some problems. In systems with AMD processors (subject only to Specter), Microsoft patches for Windows caused a cyclic restart, a "blue screen of death" and other malfunctions. Later it turned out that AMD was a bit confused with the documentation, which was sent to the developers of the patches. In some cases, updates came into conflict with antivirus and other security software, also causing BSoD.
In the published report, Intel focuses on the fact that no case of a successful attack using Meltdown and Specter is known.
Source: Intel