What is a VPN and proxy server, and how they help to bypass website blocking

to help him with a question:
-Dad, it's time you knew
What is a "proxy".
During the last two weeks the Ukrainian vocabulary was enriched with words unknown before: proxy server and VPN. If these words used to be spoken by system administrators, programmers or advanced users, now you hear only in the street, on public transport, in offices and cafes about the need to download and install a VPN. What is the reason for such a keen interest in VPN and proxy servers? And the reason is very simple - to bypass the blocking of banned social networks and services. All Ukraine already knows about decree 133/2017 President of Ukraine Petro Poroshenko "On application personal special economic and other restrictive measures (sanctions)". This decree really stirred everyone up. According to the decree, social networks such as VKontakte and Odnoklassniki were banned, as well as all services of Yandex and Mail.ru. And, needless to say, our fellow citizens had e-mail boxes on Yandex and mail.ru, even some people used cloud mail.ru to store files, negotiated and conducted business with the help of these email services. I am not talking about VK, where they listened to music for free, played games, communicated in groups. They used to find classmates, relatives and acquaintances lost in the expanses of the former USSR in Odnoklassniki. Now they will have to give it all up. I do not want to talk about why they did it and whether they did it correctly. A fact is a fact. The law exists and it has to be obeyed.
It's here that journalists and advanced users started to talk about some kind of proxy server and VPN. People started to ask what kind of VPN thing is it? What is it for and how to use it? Let's find out everything about proxy servers and VPN technology, how they work, what benefits do they bring? Is it safe to use free VPN services and proxy servers?
What are proxy servers and how to use them?

The main function of a proxy server is to send requests from its IP address, which allows you to completely or partially hide your real IP address. A distinction must be made between anonymous and transparent proxy servers. The difference between them is substantial: anonymous ones completely hide the computer address, and transparent proxies pass it in headers which become available for system administrators of web-sites. By using proxy servers you may easily get to a site which is inaccessible from your IP-address, at the same time the masking will enable you to protect your private information from prying eyes.

It is worth noting that proxy servers are needed to mask (hide) the true IP address, to be able to view sites blocked for a region or a specific user, as well as to hide the fact of visiting such sites. There are 2 ways to configure a proxy server in Windows 10. The easiest is through Settings-Network and Internet Proxy, where the ISP proxy server with your real IP address is already prescribed automatically.
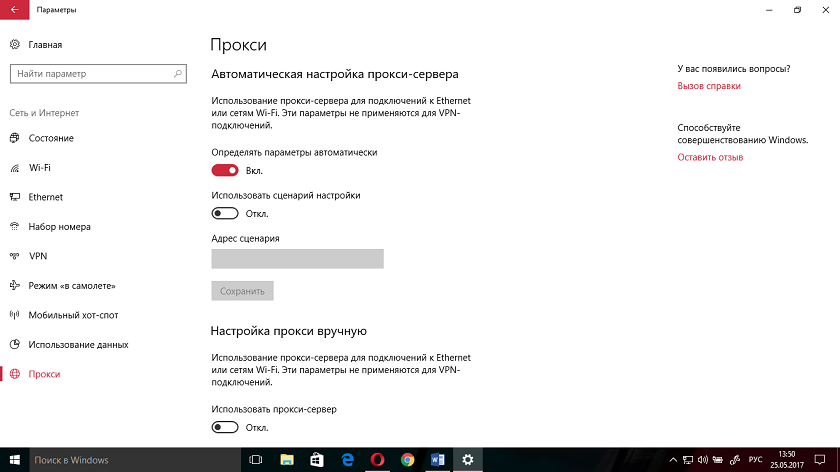
If you want to get round, for example, blocking of V Kontakte or Odnoklassniki, you can find such proxy server in search for it and copy or paste the corresponding numbers. Further down in the tab "Proxy" you have "Manually configure proxy" option. You'll get a proxy for Venezuela, for instance, or Australia.
.png)
You can also set up a proxy server through Control Panel. To do so, open All Control Panel items and go to the Browser Properties tab.
.png)
Here you click on Connections, and there on the Network Setting option. Again, enter the address of the proxy server and the number of ports. You can browse web sites by hiding your true IP address.
.png)
It sounds easy. But there are many pitfalls and surprises. Even those who are giving away these proxies for free say that you do it at your own risk and they don't take any responsibility for loss of data or any other damage resulting from using this information.
.png)
In other words, you are setting yourself up to be a victim of fraud. Add to this the possibility to download botnet proxy-servers when your PC will be a puppet in the hands of skilled hackers. The most important is that a proxy-server gives no protection, you remain "visible" for intruders and that means all the data you exchange on the Internet. And, on top of that, working with proxy servers requires a certain skill to set precise settings. So think before you install a proxy server.
What are VPNs? How to work with them?
The most important alternative to proxy servers is undoubtedly VPN (Virtual Private Network). It is both more reliable, with good security and encryption capabilities. According to Wikipedia, VPN is the generic name for technologies that allow one or more network connections (a logical network) over another network (e.g. the Internet). Simply put, when you try to go online, a kind of "tunnel" is formed between your PC and the rest of the Internet, which prevents any outside attempts to get in. By accessing any website, you are visible to the system administrators not under your IP address, but under a completely different one, from a different country that you can choose on your own.

VPN services can be free or paid. Today we will talk about the most popular free VPN services, their settings and features, as well as the problems you may have. I'll also talk about browsers with built-in VPN, app services that you can install in Windows 10, and browser extensions like Google Chrome.
Opera with built-in VPNIn my opinion, this is the chicest and easiest solution if you are an inexperienced PC user or don't want to bother with downloading and configuring browser services and extensions. The Opera browser developers have already taken care of you by embedding a VPN in their child. Enabling this service is very simple. All you need to do is to download and install the browser, then go to the menu, where in Settings you can find the option Security.
.png)
Now it is enough to find VPN item and set the slider to Enable.
.png)
Immediately next to the search bar it will say VPN. Now you can turn VPN on/off and select the country which IP address you are going to use.
.png)
It's worth noting that there are only five such countries in the list, but you can use unlimited Internet traffic. Remember also that the use of VPN-connection will significantly reduce the speed of the connection, so it is better not to turn it on unless necessary.
Where to get: www.opera.com/ru
Tor Browser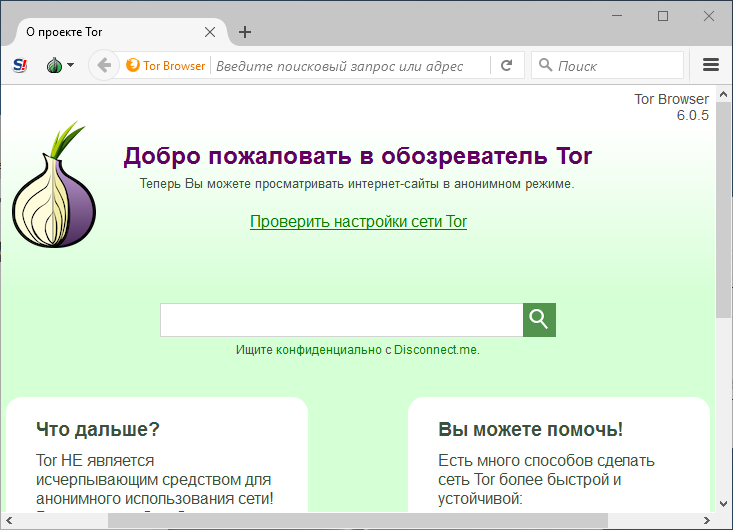
The most mysterious and enigmatic browser, which is much talked about, but few people use it. Rumor has it that it was allegedly created in the depths of some military department of the U.S., but for some unknown reason, they decided to abandon it and the rudiments of the technology Tor was quite unexpectedly made available to the public. Of course, hackers and advanced users got interested right away. About the browser they write that it is very safe and provides protection.
The onion in the logo of the Tor browser is not just for fun, as it turns out. The developers call it onion routing. There are three nodes for the operation of the browser, which belong to supporters of the browser (though no one knows who they are yet). The Tor Browser sends a packet to the first node and it contains the encrypted address of the second node. The first node knows the key for the encryption and, having learned the address of the second node, forwards the packet there. The second node, having received the packet, has the key to decrypt the address of the third node. That way, it is impossible to tell from the outside exactly what website you have ended up opening in your Tor Browser window. A bit like peeling an onion, isn't it?
Seems nice and clear, but only the routing is encrypted, not the contents of the packets being sent. Where's the guarantee that all along the path of your packet, your data can be stolen. You're not going to encrypt everything!!!
There are a few other unpleasant things about using the Tor Browser. Your ISP can figure out that you are using this particular browser. They will not know where you have been and what you have downloaded/downloaded, but the very fact that you are hiding something can have unpleasant consequences. Also, be prepared for the speed of connection and data transfer to be significantly different from that stated by your provider.
PLEASE NOTE Recent days on the Internet there are offers to download browser FreeU, which allegedly will help you bypass blocking of prohibited social networks and services. In reality it is a virus browser by means of which Mail.ru Group distributes its services which arbitrarily install themselves on your device, altering the registry settings. They may lead to malfunction of your PC and loss of personal data. Be vigilant!
Where to get: www.torproject.org
VPN extensions for Google Chrome
If you don't want to download a new browser, study it and use it later, you can safely use your favorite Google Chrome. There are a lot of VPN-extensions for it in Google Play. I will tell you only about a few of them, but it is up to you to decide which one to use.
HotspotShield Free
.png)
One of the most famous VPN extensions for Google Chrome. It is very easy to install from the Chrome plugin store.
.png)
and in just a couple of seconds you will see the extension icon in the right corner of your browser. Click on it and click on Connect.
.png)
All extension is installed and now your IP address will not be the one assigned to you by your provider. However, the free version only allows you to use servers located in the USA, Canada, France, the Netherlands and Denmark. You get unlimited internet traffic and naturally access to blocked sites.
Like any other browser extension, this VPN extension will slow down your device a bit. And you'll have to get used to ads and offers to buy paid keys from the manufacturer of the extension.
Where to get: chrome.google.com
Hola

This is also a free VPN service that gives you unlimited Internet traffic and a pretty good data rate. It's a regular, no different from other extensions like it. It's simple to use, easy to set up, no registrations whatsoever.
.png)
.png)
It would seem that everything is good and everyone is happy. But about this VPN-service an unpleasant scandal recently broke out . It was accused of selling user traffic and allegedly containing vulnerabilities related to remote code execution. Most users were wary of this information. As a result, it hit the popularity of this VPN service.
Where to get: comparite.ch/vpnchrome
Touch VPN
Another one of the free VPN extensions that is very easy to install and use. The developers have made sure that even an inexperienced user can use their product. No registration, no traffic restrictions, a good selection of servers around the world.
.png)
Everything is simple and straightforward. Judging by user reviews, compared to other VPN applications Toutch VPN is much more economical because it consumes less energy. There is, however, one significant unpleasant nuance - the speed of connection and data transfer. This is where this extension loses to its competitors.
Where to get: chrome.google.com
SurfEasy

Widely known in the circles of advanced users VPN-extension. The free version of SurfEasy Free VPN allows you to connect up to 5 devices and get 500 MB of encrypted data for free for each month. Before you can install this extension, you'll have to register.
.png)
It will take some time, but I don't like it. I do not like to throw my data on the Internet, plus too often they come from advertising and all sorts of nonsense to my email address.
Overall, the service is quite nice, fast and easy to manage, keeping your online activity safe and private in your web browser, when using email and any other programs. Some people I know love it. For me, I found it a bit too intrusive. But this is a matter of taste and priorities.
Where to get: chrome.google.com
ZenMate VPN

German origin of this VPN-extension will give you the ability to automatically activate a secure connection when you access certain sites, which eliminates the need to do it every time manually.
Disappointed little choice of countries, which servers you can use. The registration and popup offer to buy Zenmate Premium also bothers me.
.png)
The speed of this VPN-server also desires better. The choice of countries is very poor, you can expand it, but then you have to buy Premium. Everything is compensated by unlimited traffic and very good data protection.
Where to buy: chrome.google.com
TunnelBear

And finally, the most popular among advanced users Canadian VPN service - TunnelBear with a funny bear as a mascot. You can read a lot of enthusiastic reviews about it. The service does not record users' actions on the network, and if the connection to the server is interrupted for any reason, TunnelBear blocks all traffic until the connection is restored. The extension works reliably, stably and quickly, provides security even in public places and excellent support if you need it. The developers assure that the basis of TunnelBear's philosophy is the belief that everyone should be able to access all information anonymously and safely.
After downloading, you will have to go through the registration procedure, after which you get 500 MB per month, which of course can be expanded, but for an additional fee.
.png)
Where to get: www.tunnelbear.com
In a nutshell
As you can see, there is nothing complicated and scary about these proxy servers and VPN services. You can change the settings of a proxy server, download a browser supporting a VPN or install extensions in your favorite browser. There are still VPN clients for Windows 10 both paid and free. For example, I've been using a paid VPN server for over 2 years now. In the following article, I will share my experience of using just such VPN client and talk about its advantages over free solutions. Remember, it is up to you to determine what information about you, your loved ones and your work gets on the Internet. Your anonymity and privacy of your data depends on how careful you are on the web.
For those who want to know more
- Nothing to find: Ukraine bans Yandex
- Beginner paranoiac's guide, or Some tips on information security
- "VKontakte" released instructions on how to bypass blocking
- The mothballed south: what happens to mobile communications and the Internet in Crimea
- How to use Spotify, if you do not live in the USA and not in Western Europe